The Vigilance Loop is more than a security concept. It is a discipline that ties every security decision to business outcomes. In this white paper I explain how continuous security delivers true ROI. The Vigilance Loop requires constant feedback, measurement, and adaptation to tomorrow’s threat landscape. It is not a single tool or technique. It is a living architecture that grows with the enterprise. This is security as a mechanic of resilience, not a collection of point solutions.
The loop starts with detection and ends with evidence. It feeds analytics back into design, policy, and funding decisions. Executives need a frame that links risk reduction to tangible business value. The Vigilance Loop provides that frame. It emphasizes speed, precision, and accountability. In short, it makes security a strategic driver, not a cost center.
This paper defines a practical, ROI driven approach. It blends people, process, and technology into a coherent cycle. It introduces a new model called The Resilience Maturity Scale. It also offers an actionable audit and a data driven measurement suite. The result is a defensible plan that reduces risk while preserving agility. The ROI is not only financial. It is operational, reputational, and strategic. The Vigilance Loop makes all of this achievable.
The Vigilance Loop: Continuous Security Drives True ROI
Paragraph 1
Security teams must operate as a continuous learning engine. The Vigilance Loop links threat awareness to architectural choices. It relies on continuous instrumentation, rapid feedback, and decisive action. A loop that learns accelerates calendar risk reduction. It shifts the posture from reactive to proactive. In practice, this means automated monitoring, near real time policy enforcement, and fast remediation cycles. The business gains when risk is reduced at the pace of business changes, not in quarterly reports alone.
Foundations of the Vigilance Loop
Paragraph 2
At the core, the loop rests on continuous feedback, data integrity, and rapid experimentation. Teams collect telemetry from identity, network, application, and data layers. They fuse that data into actionable insights. Security design decisions align with product roadmaps and incident response playbooks. This alignment produces operational resilience and predictable risk reduction. The cycle is never paused by a vendor contract or a tool upgrade when security leadership holds the reins.
Operational ROI Signals
Paragraph 3
The loop translates into measurable ROI by linking outcomes to business metrics. Security incidents per unit of production, mean time to detect, and time to containment become leading indicators. The best models show how security controls enable faster release cycles with lower risk. When executives see traceable improvements in uptime, customer trust, and regulatory posture, the ROI becomes obvious. The loop finally makes security a driver of growth rather than a barrier to delivery.
Measuring ROI in the Vigilance Loop Across People and Tech
Paragraph 1
ROI in security must be both quantitative and qualitative. The Vigilance Loop treats people and technology as equal contributors. The measurement framework requires data from SOC tooling, development pipelines, and business outcomes. It also requires leadership discipline to translate metrics into decisions. The aim is to reduce risk exposure while enabling fast, reliable change. This is where ROI becomes a policy decision as well as a technical one.
People Metrics and Cognitive Load
Paragraph 2
Teams perform better when workload is predictable and information is actionable. The model tracks workload balance, alert fatigue, and decision latency. Training and certification programs become investments that compound across the enterprise. Managers must ensure that dashboards emphasize risk reduction in clear terms. When analysts can see a direct link between effort and incident reduction, the motivation to improve grows. The focus should be on sustainable capacity rather than heroic responses.
Technology Metrics and Automation ROI
Paragraph 3
Automation is the lever that multiplies human capability. The metrics include automation coverage, remediation speed, and policy accuracy. The best outcomes come from automating routine tasks while preserving human oversight for complex decisions. The ROI is visible when automated controls block attacks without human intervention and when developers ship features with built in security guards. Ultimately, the objective is to shrink risk carrying cost while preserving velocity.
The Adversarial Mindset and Cognitive Load
Paragraph 1
Attackers exploit psychology and operational friction. Understanding adversarial methods helps design defenses that resist disruption. The Vigilance Loop treats attacker behavior as a measurable variable. It uses threat modeling, red teaming, and adversary simulations to stress the architecture. The result is a security posture that anticipates moves and reduces surprise. The ROI appears as fewer compromises and faster recoveries in hostile scenarios.
Understanding Adversarial Psychology
Paragraph 2
Adversaries chase weak signals, timing windows, and fragile processes. Defenders must close those gaps with resilient patterns and layered controls. The cognitive load on defenders should stay manageable. If teams burn out, risk rises because vigilance declines. The architecture should push decision points to automation where possible. Training should focus on critical thinking and rapid hypothesis testing rather than memorization of playbooks.
Managing Cognitive Load in Security Teams
Paragraph 3
The correct balance reduces fatigue and increases precision. Clear ownership, well defined runbooks, and consistent validation routines matter. The best programs use progressive disclosure of risk signals. They filter noise and present only the most relevant alerts. Teams decide faster because the signal to noise ratio improves. The ROI shows up as lower burnout, faster mean time to respond, and more reliable risk ratings across the organization.
The Resilience Maturity Scale: A Model for ROI
Paragraph 1
The Resilience Maturity Scale provides a practical lens for ROI. It maps capability progression from basic containment to adaptive, proactive resilience. The scale links maturity to cost of control, risk exposure, and business agility. Each level implies specific investments and measurable outcomes. The model helps executives prioritize funding without delaying critical improvements. It also clarifies the relationship between resilience and return.
Overview of the Scale
Paragraph 2
Level 1 denotes basic containment with manual processes. Level 2 adds repeatable playbooks and some automation. Level 3 achieves integrated data flows and cross domain orchestration. Level 4 delivers proactive defense with continuous testing. Level 5 enables adaptive responses and resilience as a service. The path between levels is not binary; it is a continuum influenced by people, process, and technology. The framework helps governance align with risk appetite.
Levels and Implications
Paragraph 3
Advancing through the levels yields diminishing marginal risk but rising business value. The biggest gains occur when people responsibilities shift from firefighting to prevention. The ROI arc reflects fewer incidents, faster recovery, and improved service levels. As maturity grows, security becomes a strategic capability tied to product velocity. The model informs decisions about investments, outsourcing, and in-house capability building. It also clarifies how to measure maturity with objective indicators rather than anecdotes.
Architecture Patterns: Zero Trust, API Hardening, and Cryptographic Agility
Paragraph 1
Architecture choices determine resilience. The Vigilance Loop thrives on disciplined patterns that reduce attack surface and improve threat visibility. Zero Trust, API hardening, and cryptographic agility form a powerful trio. These patterns limit lateral movement, enforce secure interfaces, and limit exposure of data keys. The result is a more trustworthy surface for the business to operate within.
Zero Trust in Practice
Paragraph 2
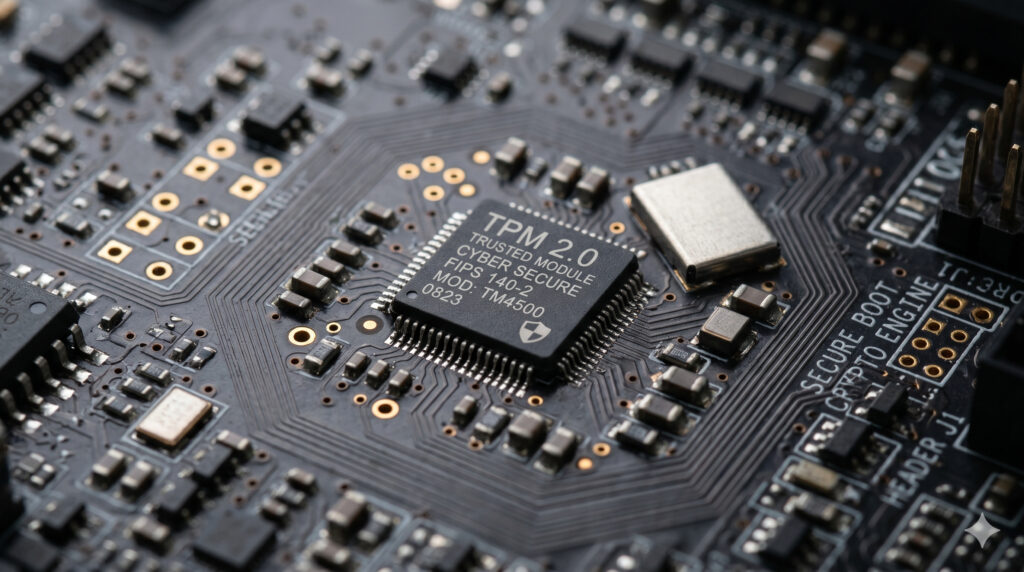
Zero Trust enforces identity and authorization at every boundary. It reduces implicit trust by requiring context for each access decision. Micro segmentation limits blast radius. Constant verification and continuous reauthentication reduce risk. The model supports secure access for SaaS, cloud workloads, and on premise resources. It also improves compliance posture by making access policies explicit and auditable.
Cryptographic Agility and Key Management
Paragraph 3
Cryptographic agility allows quick adaptation to new standards and threats. It requires modular crypto services, formal key rotation, and robust storage practices. The approach minimizes the risk of keys being compromised during upgrades. It supports post quantum readiness and diverse cryptographic algorithms. The ROI includes reduced key management friction and greater trust in inter service communications.
Data Driven ROI Metrics and Threat Tables
Paragraph 1
Security ROI is most credible when based on data. The Vigilance Loop uses a structured set of metrics that tie threat landscapes to control effectiveness. The model translates security posture into board level language. It focuses on risk reduction, velocity, and cost efficiency. With the right data, leadership can make investment decisions that yield measurable gains.
Quantifying Risk and Control Effectiveness
Paragraph 2
Metrics include threat coverage, mean time to detect, and mean time to recover. The framework also tracks risk exposure over time and cost per incident averted. It is essential to connect low level telemetry to business outcomes such as uptime, customer satisfaction, and regulatory compliance. By linking technical metrics to business goals, ROI becomes tangible.
The Architect’s Defensive Audit
Paragraph 1
An architect must continuously audit the defense. The audit translates strategy into executable steps. It also ensures that the controls address real threats and align with business priorities. The audit framework integrates risk, design, and testing in a single loop. It makes governance practical and auditable.
Executive Summary Checklist
Paragraph 2
The checklist consolidates critical decision points. It covers risk appetite, data classification, and key policy anchors. It requires cross functional sign offs and evidence of control efficacy. The list is short enough to be actionable but comprehensive enough to cover major domains. It drives disciplined funding and prioritization decisions.
Operational Audit Table
Paragraph 3
The executive summary table distills the audit outcomes into a readable format. It tracks control status, responsible owner, and time to implementation. It is designed for fast executive review and long term traceability. The table supports governance reviews and demonstrates ROI alignment.
The Path to Sustainment: Governance, Culture, and Investment
Paragraph 1
Sustainment requires governance rigor, cross functional alignment, and ongoing investment. The Vigilance Loop thrives when security is embedded in product teams and executive strategy. Governance ensures that risk decisions reflect business priorities. It also protects against scope creep and budget drift. The aim is to keep resilience a living capability rather than a static plan.
Governance, Funding, and Compliance
Paragraph 2
Strong governance translates risk findings into funding decisions. The board receives clear risk narratives and ROI projections. Compliance requirements become a baseline for capability, not a barrier. Investment prioritizes automation, incident readiness, and secure development lifecycles. This alignment keeps security budgets predictable and connected to business velocity.
Culture, Training, and Continuous Improvement
Paragraph 3
Culture drives sustained security. Training elevates security literacy, not just tool proficiency. Teams practice secure coding, threat modeling, and post incident reviews. The organization learns from every breach or near miss, and that learning feeds product design. The ROI emerges as safer products, happier customers, and a stronger market position.
Conclusion – Vigilance Loop
The Vigilance Loop reframes security as an ongoing performance metric. The ROI of continuous security is the cumulative effect of disciplined measurement, disciplined design, and disciplined action. By integrating people, process, and technology, organizations achieve resilience that scales with growth. The Resilience Maturity Scale provides the framework to guide investments and demonstrate tangible value to stakeholders. Executives should view security not as a cost but as a strategic leverage point for sustainable advantage. The loop must be maintained, funded, and practiced with the same rigor as core business processes